In this blog, we will focus on what do you mean by Central, Network, and Distributed systems along with Issues while designing a distributed system. We will also be covering Distributed Shared Memory along with coherence protocols. We will be covering the architecture of Distributed File Systems along with design Issues.

A.Centralized System?
In a centralized system, all users are connected to a central network owner or “server”. The central owner stores data, which other users can access, and also user information. This user information may include user profiles, user-generated content, and more. A centralized system is easy to set up and can be developed quickly.
In a centralized system, all users are connected to a central network owner (i.e server). The central owner stores data, which other users can access, and also user information. A centralized system is easy to set up and can be developed quickly.
When to use Centralized System?
Majorly used to for Resource Management. For example,
- Process Management
- Memory Management
- I/O Management
- File Management
Advantages of Centralized system,
- Simple deployment
- Can be developed quickly
- Affordable to maintain
- Practical when data needs to be controlled centrally
Disadvantages of Centralized system,
- Prone to failures
- Higher security and privacy risks for users
- Longer access times to data for users who are far from the server
B.Network System?
A system that facilitates to connect and communicate various autonomous computers over a network. An Autonomous computer is an independent computer that has its own local memory, hardware, and O.S. It is self capable to perform operations and processing for a single user.
When to use Network System?
Majorly used for sharing of resources between the systems i.e Interoperability. For example,
- Remote access
- Information exchange
- Network browsing
Features of Network OS,
- Environment users are aware of multiplicity of machines.
- Control over file placement is done manually by the user.
- No implicit sharing of loads.
- Performance is badly affected if certain part of the hardware starts malfunctioning.
- Remote resources are accessed by either logging into the desired remote machine or transferring data from the remote machine to user’s own machines.
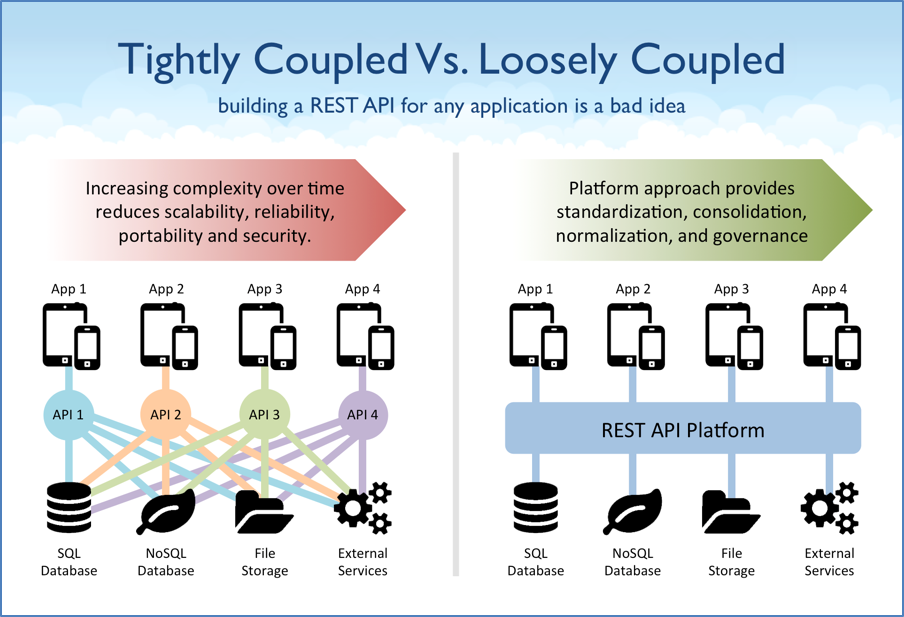
Here Tightly coupled is an example of Network Operating system and Loosely coupled is an example of distributed systems.
C.Distributed System?
A distributed system is defined as one in which components at networked computers communicate and coordinate their actions only by passing messages. It is a collection of independent computers that appear to the users of the system as a single computer.
Single computer view of multiple heterogeneous computer systems. i.e global view of Computational power, file system, name space, etc.
Features of Distributed system,
- Environment users are not aware of multiplicity of machines.
- It can be done automatically by the system itself.
- Sharing of loads between nodes (load balancing).
- It is more reliable or fault tolerant i.e. distributed operating system performs even if certain part of the hardware starts malfunctioning.
- Users access remote resources in the same manner as they access local resources.
Advantages of Distributed Systems,
- Data sharing: Allow many users to access to a common database.
- Resource Sharing: Expensive peripherals such as color laser printers, photo-type setters and massive archival storage devices are also among the few things that should be sharable.
- Communication: Enhance human-to-human communication, e.g., email, chat.
- Flexibility: Spread the workload over the available machines
Disadvantages of Distributed systems,
- Network Problem
- Network Saturation
- Malfunctioning of network
- Security
- Security violation since the private data are visible to others over the network
Distributed Computing System Models?
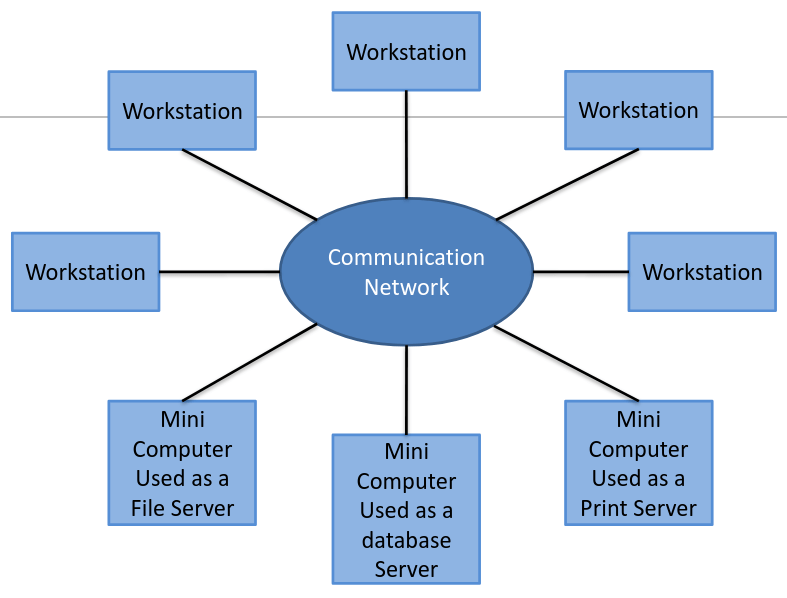
A. Mini computer Model:
An extension of Time sharing system,

- User must log on his/her home minicomputer.
- Thereafter, he/she can log on a remote machine by telnet.
For Resource sharing
- Database
- High-performance devices
Example: ARPAnet
B. Workstation Model:
1.Process migration
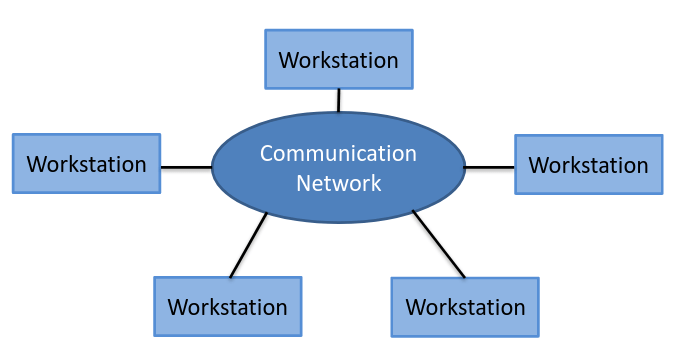
- Users first log on his/her personal workstation.
- If there are idle remote workstations, a heavy job may migrate to one of them.
2.Problems:
- What if a user log on the remote machine?
- How to find an idle workstation?
- How to migrate a job?
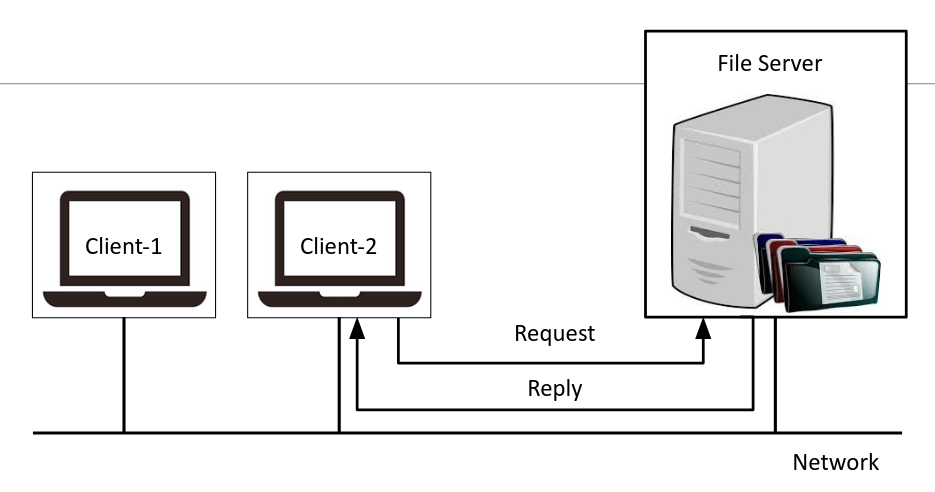
C. Work station server model
1.Client workstations
- Disk less
- Graphic/interactive applications processed in local.
- All file, Print, HTTP and even cycle computation requests are sent to servers.
2.Server minicomputers
- Each minicomputer is dedicated to one or more different types of services.
3.Client-Server model of communication
- RPC (Remote Procedure Call)
- RMI (Remote Method Invocation)
- A Client process calls a server process function.
- No process migration invoked
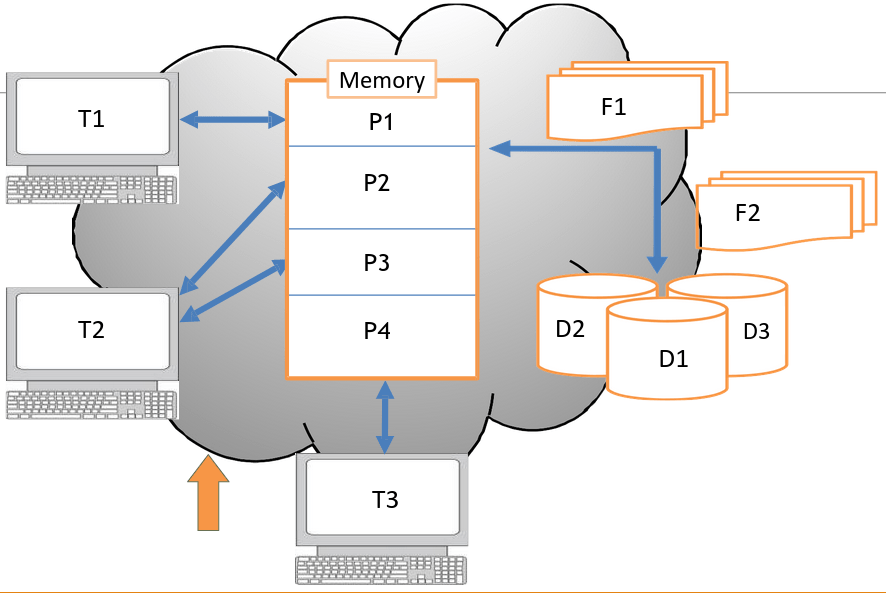
D. Processor-Pool Model
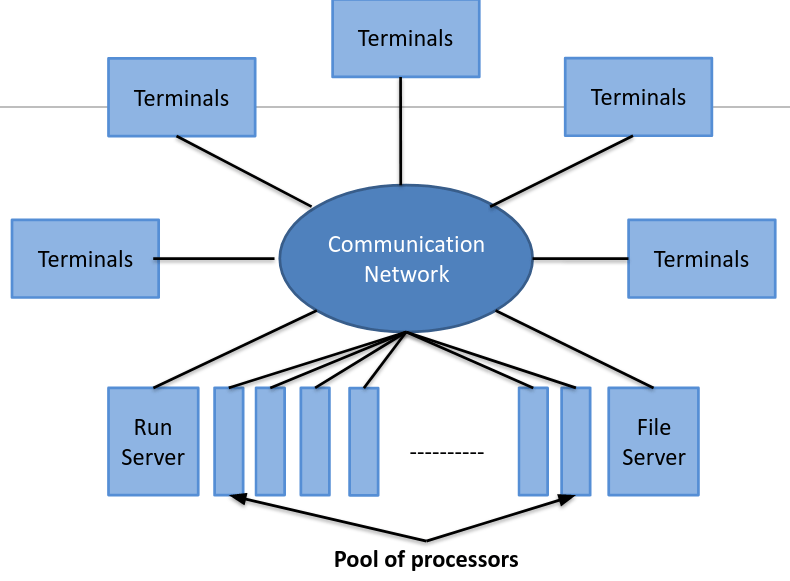
1.Clients:
- They log in one of terminals
- All services are dispatched to servers.
2.Servers:
- Necessary number of processors are allocated to each user from the pool.
Better utilization of resources.
Used for better utilization of resources. Example: Web Search Engines
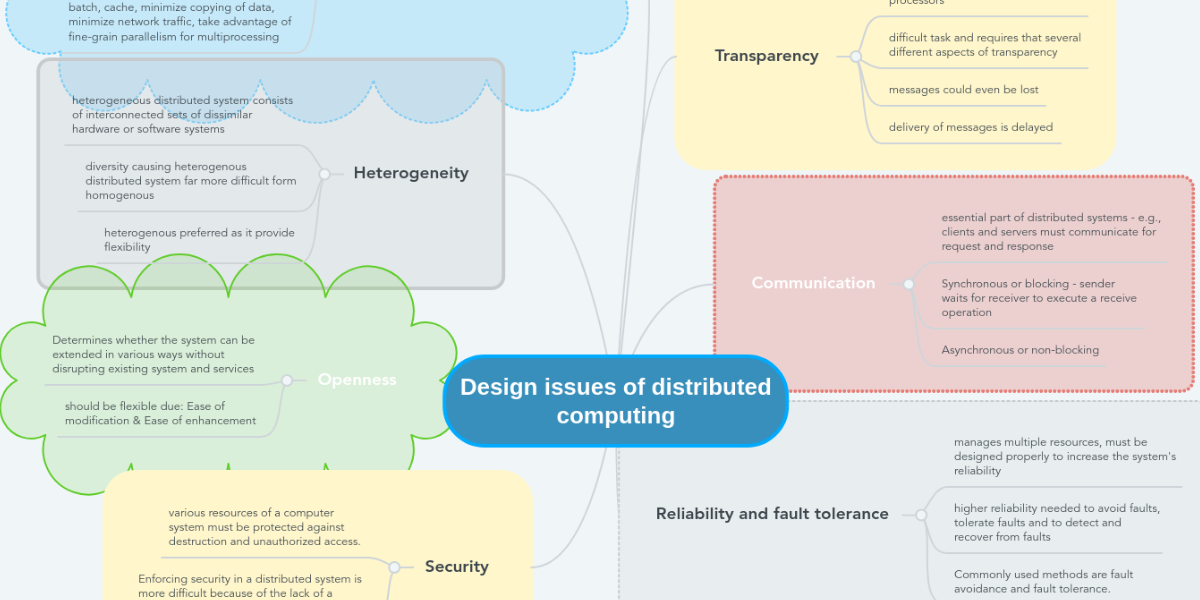
Issues in Designing a Distributed System?
1.Transparency:
The main goal of Distributed system is to make the existence of multiple computers invisible and provide single system image to user.
While users hit search in google.com, They never notice that their query goes through a complex process before google shows them a result. There are the following types of transparencies
- Access Transparency
- Location transparency
- Replication Transparency
- Failure Transparency
- Migration Transparency
- Concurrency Transparency
- Performance Transparency
- Scaling Transparency
2.Reliability:
Distributed systems are expected to be more reliable than centralized systems due to the existence of multiple instances of resources. System failure are of two types:
- Fail-stop: The system stop functioning after detecting the failure.
- Byzantine failure: The system continues to function but gives wrong results.
The fault-handling mechanism must be designed properly to avoid faults, to tolerate faults and to detect and recover from faults.
A. Fault tolerance:
- Redundancy technique: To avoid single point of failure.
- Distributed control: To avoid simultaneous functioning of the servers.
B. Fault detection and recovery:
- Atomic transaction.
- Stateless server.
- Acknowledgment and timeout-based retransmissions of messages.
3. Flexibility:
The design of Distributed operating system should be flexible due to following reasons:
- Ease of Modification: It should be easy to incorporate changes in the system in a user transparent manner or with minimum interruption caused to the users.
- Ease of Enhancement: New functionality should be added from time to time to make it more powerful and easy to use.
4.Performance:
A performance should be better than or at least equal to that of running the same application on a single-processor system. Some design principles considered useful for better performance are as below:
- Batch if possible: Batching often helps in improving performance.
- Cache whenever possible: Caching of data at clients side frequently improves over all system performance.
- Minimize copying of data: Data copying overhead involves a substantial CPU cost of many operations.
- Minimize network traffic: It can be improved by reducing inter node communication costs.
5.Scalability:
Distributed systems must be scalable as the number of user increases. Scalability has 3 dimensions:
- Size: Number of users and resources to be processed.
- Geography: Distance between users and resources.
- Administration: As the size of distributed systems increases, many of the system needs to be controlled.
A system is said to be scalable if it can handle the addition of users and resources without suffering a noticeable loss of performance or increase in administrative complexity.
6.Heterogeneity:
This term means the diversity of the distributed systems in terms of hardware, software, platform, etc. Modern distributed systems will likely span different:
- Hardware devices: computers, tablets, mobile phones, embedded devices, etc.
- Operating System: Ms Windows, Linux, Mac, Unix, etc.
- Network: Local network, the Internet, wireless network, satellite links, etc.
- Programming languages: Java, C/C++, Python, PHP, etc.
7.Security:
System must be protected against destruction and unauthorized access. Enforcement of security in a distributed system has the following additional requirements as compared to centralized system:
- Sender of the message should know that message was received by the intended receiver.
- Receiver of the message should know that the message was sent by genuine sender.
- Both sender and receiver should be guaranteed that the content of message were not changed while it is in transfer.

3 thoughts on “What do you mean by Distributed Systems, Shared Memory and File Systems”