Thing to know before developing your cyber security solution
According to the Cybersecurity and Infrastructure Security Agency(CISA),” Cybersecurity is the art of protecting networks, devices, and data from unauthorized access or criminal use and the practice of ensuring confidentiality, integrity, and availability of information.”. A few terms to know before going ahead,
- Privacy means maintaining confidentiality.
- Anonymity means no body knows who you are?
- Pseudonymity means using an alias.
How much of your daily life relies on technology? How much of your personal information is stored on a device or a server?
There are many risks, some more serious than others. Among these dangers is malware erasing your entire system, an attacker breaking into your system and altering files, an attacker using your computer to attack others, or an attacker stealing your credit card information and making unauthorized purchases. There is no guarantee that even with the best precautions some of these things won’t happen to you, but there are steps you can take to minimize the chances.
Here we classify risk being a combination of three factors,
- Assets are items having value to the firm such as data, servers, software, network equipment, …
- Threats are conditions that can cause damage to an asset such as cyber attack, breach of integrity attack, malware, disclosure of confidential data, natural disasters,…
- Vulnerabilities are weakness in the system design, implementation, software code or lack of preventive mechanism such as bugs, physical security, …
Risk= Vulnerablity * threat * Consequences
Our goal should be to minimise risk to an acceptable level, as eliminating all risks is not feasible.
How to make sure our data is secure?
We usually use the CIA Triad where,
- C stands for Confidentiality(“How secure is your data?”):
- You could use encryption(at rest and at transit) or firewalls or Two factor authentication.
- Failure of confidentiality occurs if someone can obtain and view the data.
- I stands for Integrity(“How correct is the information?”):
- You could use hashing of information or checksum technique during data transmission.
- Failure of integrity occurs if someone modifies the data being stored in or transit.
- A stands for Availability(“How much up time and latency is the system providing?”) :
- You could use better system design and data points or a better disaster recovery plan.
- Failure of availability occurs if the data cannot be accessed by the end user.
Usually, we have to make a trade-off between the usability of a system and the security of the system.
What do you mean by cyber attacks?
A cyber attack targets computer information systems, computer networks, infrastructures, or personal computer devices. An attacker is a person or process that attempts to access data, functions, or other restricted areas of the system without authorisation, potentially with malicious intent.
Cyberattacks can range from installing spyware on a personal computer to attempting to destroy the infrastructure of entire nations. We could categorise cyber attacks into 2 types,
- Web based Attack, attacks on an web application. These are done using,
- System based attack, attacks to compromise a computer or a computer network. These are done using,
1.Denial-of-service attack (DoS)
The attacker seeks to make a machine or network resource unavailable to its intended users by temporarily or indefinitely disrupting services of a host connected to the Internet. Typically accomplished by flooding the targeted machine or resource with superfluous requests in an attempt to overload systems and prevent some or all legitimate requests from being fulfilled.
2.Distributed denial-of-service attack (DDoS)
The incoming traffic flooding the victim originates from many different sources. This effectively makes it impossible to stop the attack simply by blocking a single source.
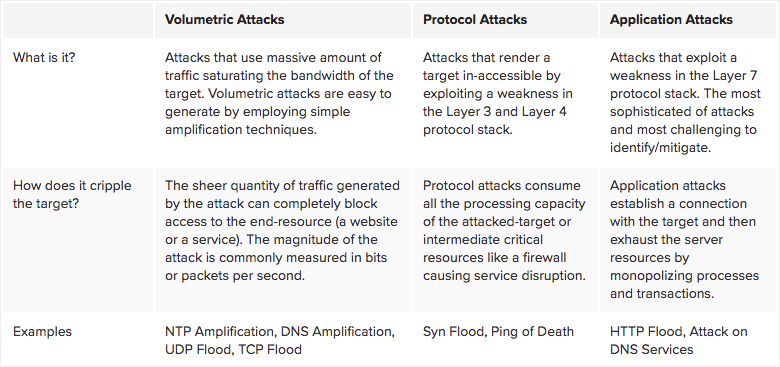
There are 3 types of DDos Attacks:
What are the signs of a DOS/DDOS attack:
- Degradation in network performance due to drastic increase in requests sent to server.
- Loss of Information from the server
- Unavailability of the server
A DoS or DDoS attack is analogous to a group of people crowding the entry door of a shop, making it hard for legitimate customers to enter, thus disrupting trade.
For more information on DOS/DDOS attack,
- https://www.cloudflare.com/en-gb/learning/ddos/glossary/denial-of-service/
- https://searchsecurity.techtarget.com/definition/distributed-denial-of-service-attack
3.Brute force attack
Used to obtain private information such as usernames, passwords, passphrases etc by repeatedly submitting different combinations of credentials, attackers can ultimately guess them correctly, and gain access to the data those credentials protect.
Common targets for brute force attacks are cracking passwords and encryption keys as well as API keys and SSH logins.
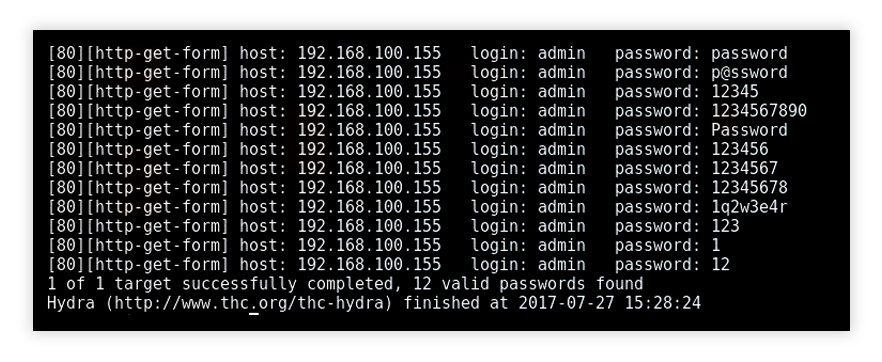
The success of a brute force attack is measured in the time it takes to successfully crack a password/credential. As password length increases, the time it takes to brute force it increases as well.
- As a key with 128-bit encryption will have 2128 combinations and 256-bit encryption will have 2256 combinations.
For more information on brute force attacks,
- https://securitytrails.com/blog/brute-force-attacks
- https://www.imperva.com/learn/application-security/brute-force-attack/
4. Session hijacking
Also known as cookie hijacking is the exploitation of a valid computer session sometimes also called a session key, to gain unauthorised access to information or services in a computer system. There are four main methods used to perpetrate a session hijack,
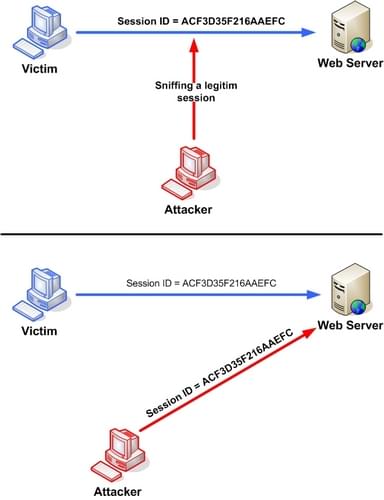
1. Session fixation: where the attacker sets a user’s session id to one known to them. For example: by sending the user an email with a link that contains a particular session id. The attacker now only has to wait until the user logs in.
2. Session side jacking: where the attacker uses packet sniffing to read network traffic between two parties to steal the session cookie. Many web sites use SSL encryption for login pages to prevent attackers from seeing the password.
Unsecured Wi-Fi hotspots are particularly vulnerable, as anyone sharing the network will generally be able to read most of the web traffic between other nodes and the access point.
3. Cross-site scripting: where the attacker tricks the user’s computer into running code which is treated as trustworthy because it appears to belong to the server, allowing the attacker to obtain a copy of the cookie or perform other operations.
4. Malware and unwanted programs can use browser hijacking to steal a browser’s cookie files without a user’s knowledge, and then perform actions (like installing Android apps) without the user’s knowledge.
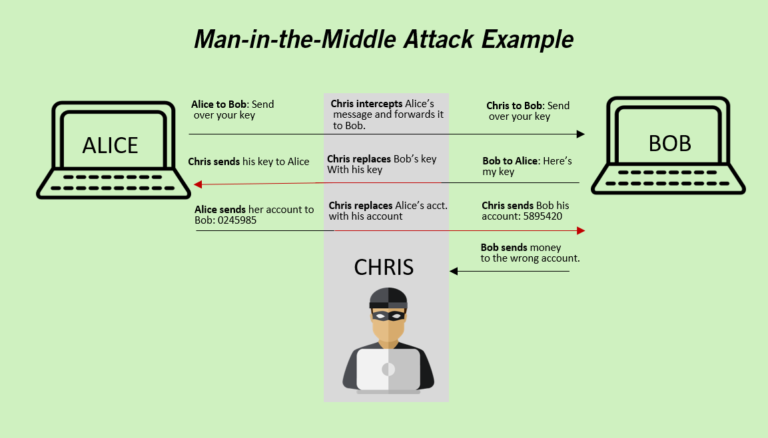
5. Man in the Middle
A man-in-the-middle attack is a type of eavesdropping attack, where attackers interrupt an existing conversation or data transfer. After inserting themselves in the “middle” of the transfer, the attackers pretend to be both legitimate participants.
This enables an attacker to intercept information and data from either party while also sending malicious links or other information to both legitimate participants in a way that might not be detected until it is too late.
Ways to prevent Man in the middle attack,
- VPN
- Network Security with IDS
- Install active virus and malware protection
- Secure your communication
- Avoid using public wifi networks
For more information on man in the middle attack,
6. SQL injection
SQL injection is a code injection technique used to attack data-driven applications, in which malicious SQL statements are inserted into an entry field for execution (e.g. to dump the database contents to the attacker).
SQL injection must exploit a security vulnerability in an application’s software, for example, when user input is either incorrectly filtered for string literal escape characters embedded in SQL statements or user input is not strongly typed and unexpectedly executed.
SQL injection is mostly known as an attack vector for websites but can be used to attack any type of SQL database.
For more information on SQL injection,
7.PHISHING ATTACKS
Phishing attacks utilize social engineering to induce users to hand up personal information such as passwords or financial information or to complete specific activities such as downloading malware or completing a wire transfer. Giving the hacker access to all vital information or control over the information.
Human nature allows phishers to take advantage of the fact that most people overlook vital warning warnings. Phishing attacks have been so successful in part due to a lack of information regarding phishing assaults in the general public.
For more information on phishing attacks,
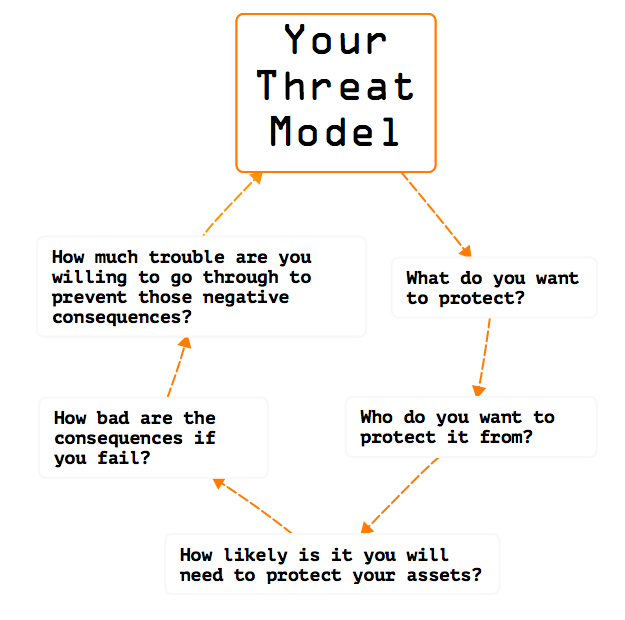
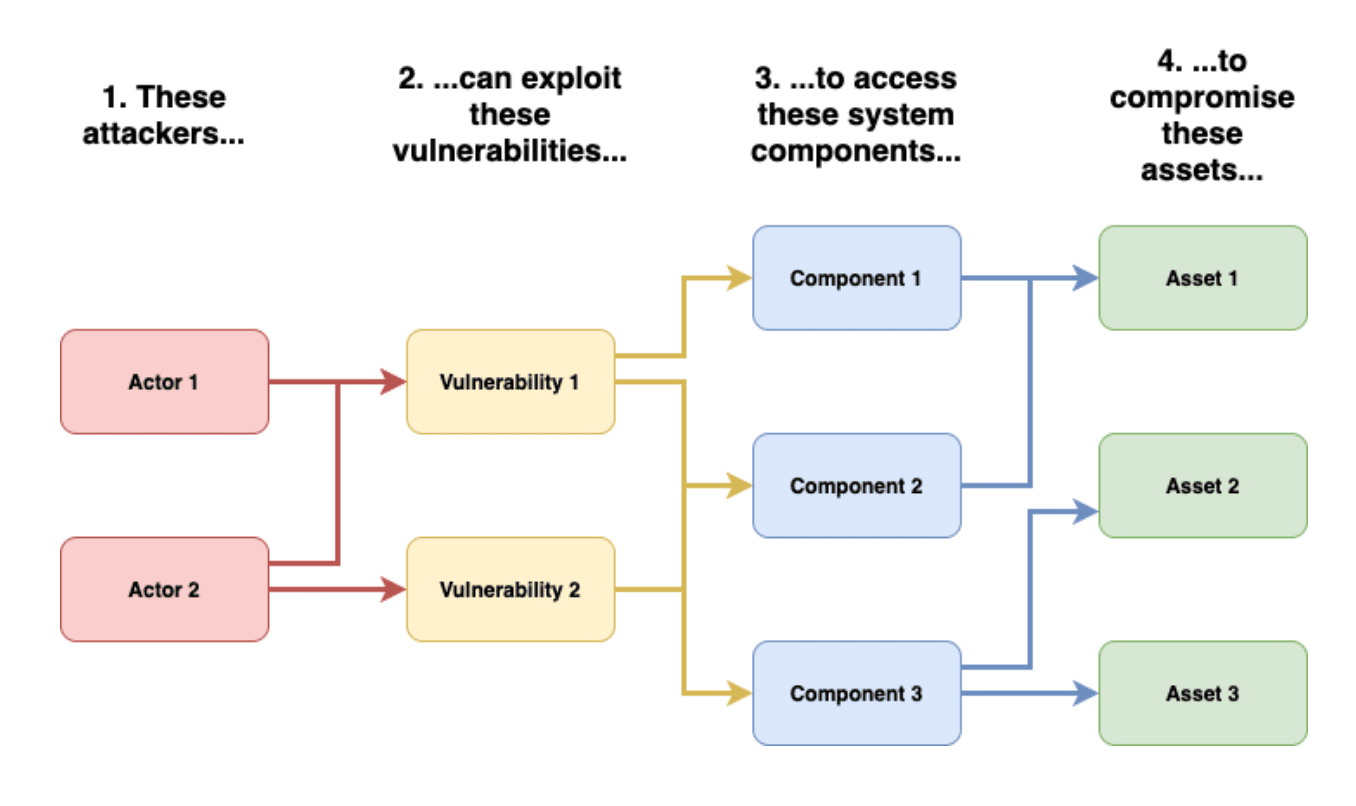
Threat Modelling?
Threat modelling refers to the process of identifying, understanding, and communicating risks and mitigation to protect something of value. It includes finding your area of vulnerability and post probable types of attacks.
It often leads to asking questions like,
- Where am i most vulnerable to attack
- What are the most relevant threats
- what could go wrong?(exception cases)
- Are there any possible bugs, and what can be done to address these bugs?
Different Threat modeling approaches
1. Software centric: Focus is on the software being built and what weaknesses and vulnerabilities are likely to be introduced in design, code, or build integration. A few questions to consider:
- How is software designed and constructed?
- What are the languages, components and run times used?
- What are the relevant coding practices followed?
How is software built and integrated with the use of software architecture diagrams such as data-flow diagrams(DFD),use case diagrams or component diagrams to identify threats to the design of the system
2. Asset centric: Focus is on assets needing protection and entrusted to a system or software(data processed by the software) & what scenarios might compromise them or lead to non-compliance. A few questions to consider:
- What are the assets entrusted to the system or software?
- What are the consequences to compromise or loss of the assets?
- How are those assets protected?
Involves the use of attack trees patterns by which an asset can be attacked.
3. Attacker centric: The focus is on profiling an attacker’s characteristics, skill set, and motivation to exploit vulnerabilities and what scenarios might attackers use to comprise the application, system, or service. A few questions to consider:
- Who is authorised and who is not?
- What privileges do users have?
- How can the software be abused?
This approach also uses attack trees or attack patterns with focus on the specific goals of an attacker, how attacks could be carried out, and how to mitigate such attacks.
Which Approach to use?
- Software centric approach is best in exposing issues in the design of a system—its focus is on the software being built
- Asset and Attacker centric approaches are important approaches to apply in threat modeling as well, but its best not to combine approaches to avoid confusion in the process.
A Recommendation would be to start with software centric approach for one release or sprint, and switch to a different approach for the next release or sprint.

To know more about Threat modelling techniques: