Things to know about Phishing attacks
As the number of cyber security attacks are growing exponentially, In 2020, approximately 75% of enterprises around the world will have experienced a phishing attack. In this blog, we will cover what do you mean by a phishing attack, the most commonly used phishing techniques, the life cycle of a phishing technique, and ways to prevent a phishing technique.
There are several ways to launch a cyber security attack. For example, we could use a denial of service attack, in which we flood a network with false queries to prevent it from responding to legitimate queries, or a man in the middle attack, in which we insert ourselves between two parties to filter and steal data, or SQL Injection, in which we insert SQL code into a server to corrupt or damaged data.
According to Verizon’s 2021 Data Breach Investigations Report (DBIR), phishing is the most common “activity variety” seen in breaches in the previous year, with phishing and/or pretexting accounting for 43 percent of all breaches. Phishing attacks are one of the most popular and significant risks on the Internet today, in which cybercriminals attempt to steal a user’s personal or financial information by employing software or social engineering. The ability to detect phishing assaults with high accuracy has always been a hot topic.
Q.What exactly do you mean by phishing attacks?
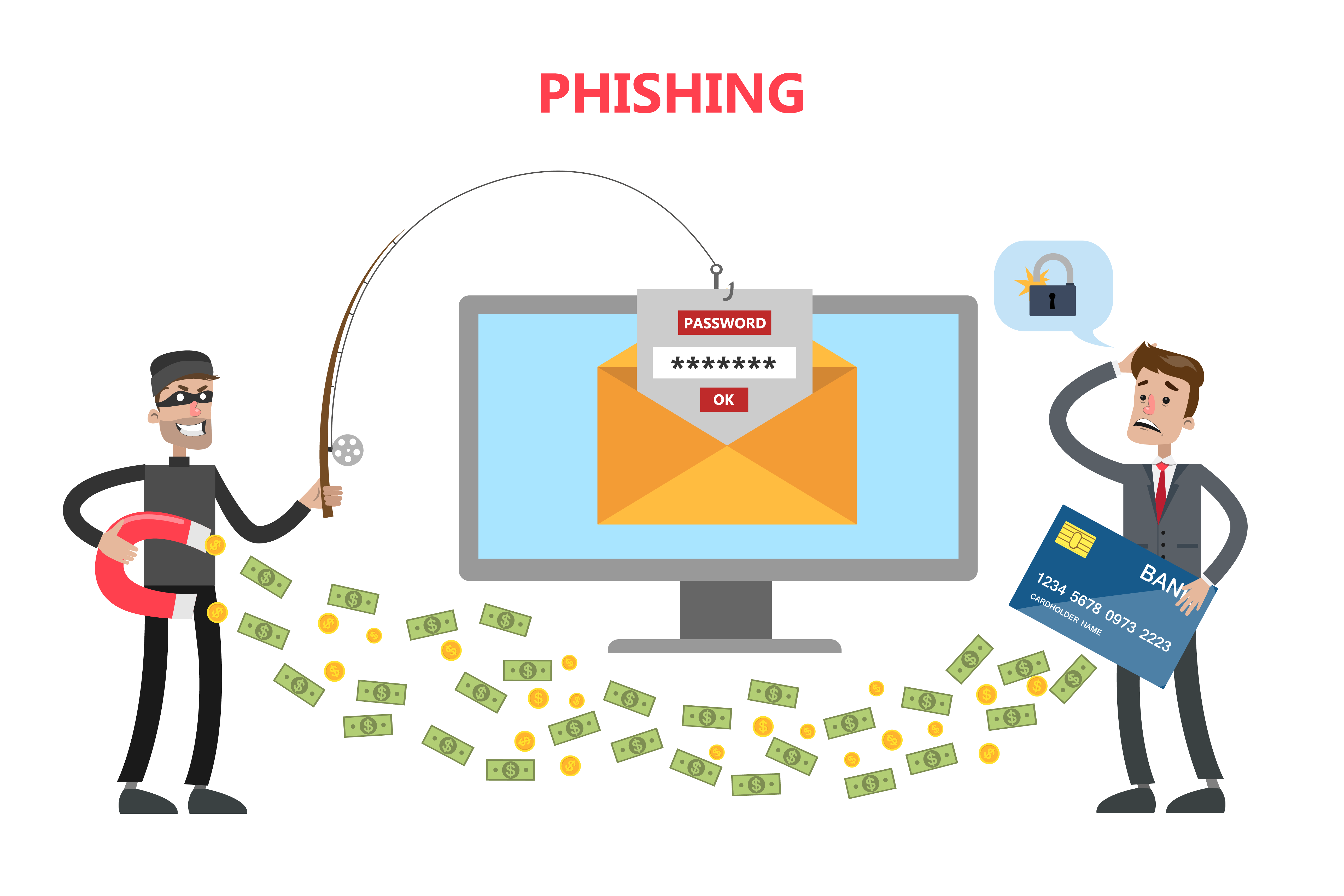
Phishing attacks utilize social engineering to induce users to hand up personal information such as passwords or financial information or to complete specific activities such as downloading malware or completing a wire transfer. Giving the hacker access to all vital information or control over the information.
Human nature allows phishers to take advantage of the fact that most people overlook vital warning warnings. Phishing attacks have been so successful in part due to a lack of information regarding phishing assaults in the general public.
While our software for detecting phishing attacks is improving, phishing attacks are also improving. New and impactful phishing attacks like spear-phishing are causing the majority of attacks on data. The phishing problem is widespread because there are numerous ways to carry out such an assault, implying that a single remedy will not suffice. Here are some of the most common phishing techniques:
- Email phishing is when a hacker impersonates a legitimate identity and sends out a big number of emails. These emails are usually crafted with a sense of urgency in the hopes that recipients would not pay attention to the specifics and will act quickly, such as clicking a malicious link that leads to a fake login page or downloading harmful software.
- Spear Phishing is when rather than mass-sending emails, hackers target specific individuals within a company with fraudulent emails. They will personalise it for the victim in order to make the victim believe they have some form of relationship/connection with the hacker.
- Whaling occurs when hackers target senior executives rather than any other employee within a corporation. Now, the chances of these emails working are slim, but the amount of data a hacker could gain from them makes it worthwhile to try. These emails frequently employ a high-pressure environment to urge their victims to click on the malicious link or attachment in order to learn additional information.
- Smishing or SMS phishing, often known as smishing, is a type of phishing attempt that uses text messages rather than email to carry out the attack. They work in a similar fashion to email-based phishing attacks:
- Clone Phishing is when a hacker generates a malicious copy of a recent communication you’ve received and sends it to you again from a seemingly trustworthy source. Attackers frequently use the pretext of re-sending the message owing to problems with the prior email’s links or attachments.
Apart from these, there are Vishing(Smishing but for voice calls), Evil Twin phishing( create a fake WiFi network to duplicate an original WiFi network to extract information using the fake network.), Social Media Phishing, and Search Engine Phishing.
A general phishing lifecycle includes the following steps assuming that the victim falls right into the phishing attack. These are the few major steps,
- Hackers identify the target company or individual and then gather information about the organization and its network during the planning and setup phase. Then they set up the attacks using a practical solution, such as a website or emails with malicious links that could lead the victim to a fraudulent website.
- Phishing entails sending faked emails to the target, posing as genuine organizations such as banks or hospitals, and requesting that the user update certain information urgently by clicking on a harmful link.
- Then the victim clicks on the fraudulent link, either malware is installed on the system, allowing the attacker to invade and change the system’s settings, or the victim’s access rights are changed. In rare circumstances, it may lead to a bogus website that requests credentials.
- Once the attackers get access to the user’s machine, the required data is retrieved, and if the user gives the attacker his account details, the attacker can now access the user’s account, potentially resulting in financial losses for the victim.
- After obtaining the necessary information, the phisher destroys all evidence, including the fake website accounts. They also seem to keep note of the degree of success of their attacks in order to improve future attacks.

How to prevent Phishing attacks?
According to the Phishing Statistics section of 2018, Verizon Data Breach Investigations Report targeted users to open 30 percent of phishing communications, and 12 percent of those users click on the malicious attachment or link. Because the majority of people are unable to identify a sophisticated phishing attempt. Before we reply to a potential phishing attempt, here are a few warning indicators to keep in mind:
- If you receive an email that appears to be genuine but comes out of nowhere, it’s likely from an untrustworthy source.
- A phishing attempt is immediately identified by misspelt words, bad syntax, or a weird turn of phrase.
- If you receive a communication that appears to be designed to make you fear and respond quickly, read it carefully.
- Never accept email attachments or click link addresses in emails from unknown senders, and double-check email addresses even if they appear to be from a known sender. Without your knowledge, malware can be installed on your computer by opening email attachments or visiting links.
- If you’re contacted about what appears to be a once-in-a-lifetime opportunity, it’s most likely a hoax.
- Consider using a Virtual Private Network (VPN), which encrypts your internet traffic and keeps all of your online activity hidden from prying eyes. Your true IP address is likewise hidden by a VPN, guaranteeing that it is not linked to your real location or identity.
Having a reliable antivirus is the next best option. It will provide you with a greater opportunity to defend yourself from these hackers and their attacks. The final alternative is to disclose a phishing attack, as relatively few employees in report phishing attacks. Before you respond to a probable phishing assault, ask yourself the following questions: Do you identify the sender? Were you expecting this individual to send you an email? Is the email appropriate for your position?, and If the sender is requesting personal information do be wary.
We can be certain of two things based on the history of phishing attacks.
- Attacks will get more sophisticated.
- Targeted ransomware will receive greater attention. As the number of spear phishing assaults rises, so does the number of smart gadgets, which present a simple means to hack information if not properly safeguarded.
For further information & stats on the phishing attacks,
- https://www.tessian.com/blog/phishing-statistics-2020/
- https://hostingtribunal.com/blog/phishing-statistics/
Papers Referred to understand Phishing attacks:

bookmarked!!, I like your site!
LikeLike