Some basic key definitions:
- Bandwidth: Data transferred per unit time. So 10 Mbps is equal to transfer of 10 million bits every second.
- Throughput: Total data transmission for a specified time range.
- Latency: Transfer delay of of data packets
- Router: It helps you connect multiple devices to the Internet, and connect the devices to each other.
- A router acts as a dispatcher, choosing the best route for your information to travel.
- Internet Protocol (IP): Is the address system of the Internet and has the core function of delivering packets of information from a source device to a target device.

Q.Is there any difference between URL, URN and URI?
- Uniform Resource Identifier: A string of characters used to identify a name or a resource on the Internet. A URI has two specializations known as URL and URN.
- Uniform Resource Locator: Specifies where an identified resource is available and the mechanism for retrieving it. A URL defines how the resource can be obtained.
- Uniform Resource Name: Uses the URN scheme, and does not imply availability of the identified resource
Both URNs (names) and URLs (locators) are URIs, and a particular URI may be both a name and a locator at the same time.

application Architecture
1.Client Server Model:
The client computer sends a request for data to the server through the internet, the server accepts the requested, process it and deliver the data packets requested back to the client. One special feature is that the server computer has the potential to manage numerous clients at the same time.
A single client can connect to numerous servers at a single timestamp, where each server provides a different set of services to that specific client. It creates a centralized network.
An example, would be my computer and the WordPress server.
2.Peer to Peer Model:
All the computers and devices that are part of them are referred to as peers, and they share and exchange workloads. Each peer in a peer-to-peer network is equal to the other peers. There are no privileged peers, and there is no primary administrator device in the center of the network.
The primary goal of peer-to-peer networks is to share resources and help computers and devices work collaboratively, provide specific services, or execute specific tasks. It creates a decentralized network.
An example would be torrent sites, as transfer of data happens from peer to peer.
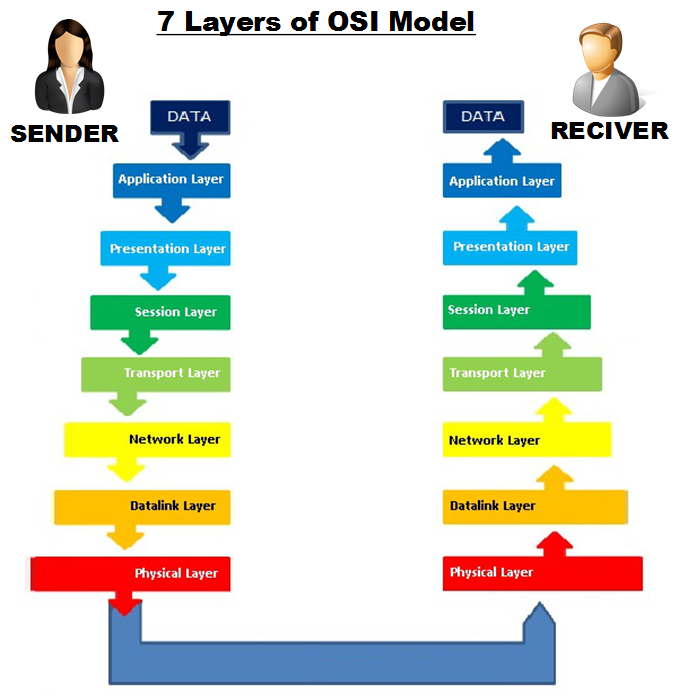
3.Open System Interconnection model(OSI Model):
The OSI model can be seen as a universal language for computer networking. It’s based on the concept of splitting up a communication system into seven abstract layers, each one stacked upon the last.

1.Application Layer:
Acts as an interface between users and software applications. Data is packed from this interaction to transmit. Application layer is responsible for the protocols and data manipulation that the software relies on to present meaningful data to the user.
2.Presentation Layer:
Preparing data by converting it into binary code, so that it can be used by the application layer. The presentation layer is responsible for translation, encryption, and compression of data.
3.Session Layer:
The time between when the communication is opened and closed is known as the session.
The session layer ensures that the session stays open long enough to authenticate, authorize and transfer all the data being exchanged, and then promptly closes the session in order to avoid wasting resources.
4.Transport Layer:
Responsible for end-to-end communication between the two devices. This includes taking data from the session layer and breaking it up into chunks called segments before sending it. The transport layer on the receiving device is responsible for reassembling the segments into data the session layer can consume. The transport layer is also responsible for flow control and error control.
- Flow control determines an optimal speed of transmission to ensure that a sender with a fast connection doesn’t overwhelm a receiver with a slow connection.
- Performs error control on the receiving end by ensuring that the data received is complete, and requesting a re-transmission if it isn’t.
5.Network layer:
Responsible for facilitating data transfer between two different networks. If the two devices communicating are on the same network, then the network layer is unnecessary. The network layer breaks up segments from the transport layer into smaller units, called packets, on the sender’s device, and reassembling these packets on the receiving device.
6.Data Link layer:
Facilitates data transfer between two devices on the same network. The data link layer takes packets from the network layer and breaks them into smaller pieces called frames.
Like the network layer, the data link layer is also responsible for flow control and error control in intra-network communication . The transport layer only does flow control and error control for inter-network communications.
7.Physical layer:
This layer includes the physical equipment involved in the data transfer, such as the cables and switches. This is also the layer where the data gets converted into a bit stream, which is a string of 1s and 0s. The physical layer of both devices must also agree on a signal convention so that the 1s can be distinguished from the 0s on both devices.
For more information on OSI model,
- https://www.youtube.com/watch?v=-6Uoku-M6oY
- https://www.freecodecamp.org/news/osi-model-networking-layers-explained-in-plain-english/
4.Transmission Control Protocol/Internet Protocol (TCP/IP) Model:
Transmission Control Protocol/Internet Protocol (TCP/IP) network provides a framework for transmitting this data, and it requires some basic information from us to move this data.
There was redundancy and repetition of functionalities in different layers in OSI Model, So we combined Application, Presentation and Session Layer into one layer called Application layer. This layer was responsible for all the functionalities of three layers.
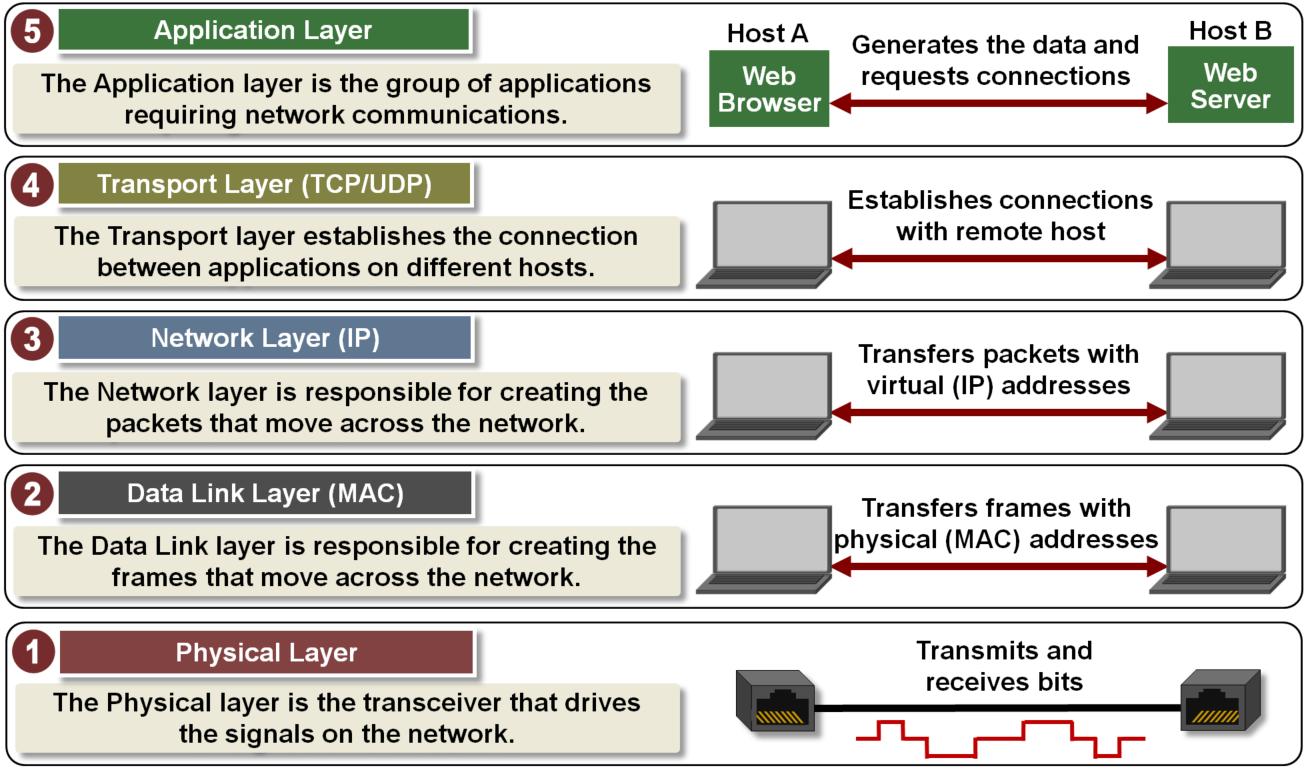
1.Application Layer:
- Responsible for the protocols and data manipulation that the software relies on to present meaningful data to the user.
- Responsible for converting data into binary code, encrypting data and compressing data, before beginning the session.
- Responsible for ensuring that the session stays open long enough to authenticate, authorize and transfer all the data being exchanged, and then promptly closes the session in order to avoid wasting resources.
2.Transport Layer:
Establishes the connection between applications running on different hosts. It keeps track of the processes running in the applications above it by assigning port numbers to them and uses the Network layer to access the TCP/IP network.
3.Network Layer:
Responsible for creating the packets that move across the network. It uses IP addresses to identify the packet’s source and destination.
4.Data Link Layer:
Responsible for creating the frames that move across the network. These frames encapsulate the packets and use MAC addresses to identify the source and destination.
5.Physical Layer:
The Physical layer encodes and decodes the bits found in a frame and includes the transceiver that drives and receives the signals on the network.

For more information on tcp/IP model,
Network Performance:
We have to minimize the Delay and Packet Loss, and maximize Throughput.
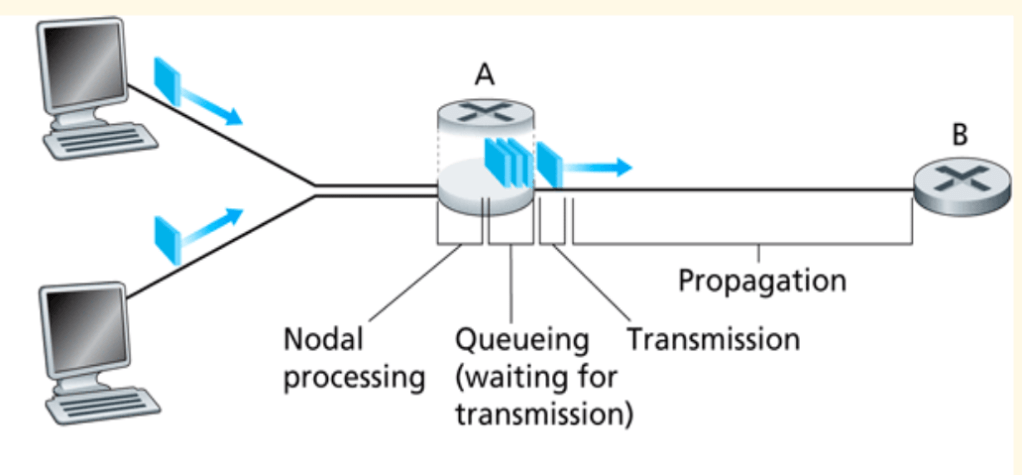
- D(proc): Between the time the packet is correctly received at the head node of the incoming link and the time the packet is assigned to an outgoing link queue for transmission.
- D(queue): Between the time the packet is assigned to a queue for transmission and the time it starts being transmitted. During this time, the packet waits while other packets in the transmission queue are transmitted.
- D(trans): Between the times that the first and last bits of the packet are transmitted.
- D(prop): Between the time the last bit is transmitted at the head node of the link queue and the time the last bit is received at the next router. This is proportional to the physical distance between transmitter and receiver.
Total Delay= D(proc)+ D(delay) + D(trans) + D(prop)
One thought on “How does modern computer networking work?”