I spent over a couple of weeks reading about Virtual Private Cloud(VPC), public and private subnets, Internet Gateway, Route tables, Network access control lists(NACLs), Security Groups, Nat Gateway, Bastion hosts, VPC peering, AWS Transit Gateway, VPN connections, AWS Direct connect, AWS Route 53 and AWS Cloud Front.
Q. What do you mean by a Virtual Private Cloud(VPC)?
A VPC resides inside of the AWS Cloud and it’s essentially your own isolated segment of the AWS Cloud itself. By default when you create your VPC, you only have access to it from your own AWS account.
It allows you to start deploying resources within your VPC, for example, different compute resources or storage or database and other network infrastructure among others and this allows you to start building and deploying your solutions within the Cloud.
It’s very simple to create a VPC,
- Give it a name, when you create your VPC
- Define an IP address range that the VPC can use and this is done in the form of a Classless Inter-Domain Routing(CIDR) block.
The CIDR block address is a range of IP addresses and this CIDR block range can have a subnet mask between a range of IP addresses from a /16 all the way through to a /28.
For more information about VPC,
- https://aws.amazon.com/vpc/?vpc-blogs.sort-by=item.additionalFields.createdDate&vpc-blogs.sort-order=desc
- https://docs.aws.amazon.com/vpc/latest/userguide/what-is-amazon-vpc.html
- https://docs.aws.amazon.com/vpc/latest/userguide/how-it-works.html
Q. What do you mean by subnets?
Subnets reside inside your VPC, and they allow you to segment your VPC infrastructure into multiple different networks. You might want to do this to create better management for your resources, or to isolate certain resources from others, or even to create high-availability and resiliency within your infrastructure.

What makes a subnet public and what makes a subnet private?
A public subnet is accessible from outside of your VPC. So essentially from the Internet. They have two IP addresses.
- They have their own internal IP address which will be within the range of the subnet,
- We assign them a public IP address as well, because to be accessible from the Internet, the instance itself has to have a public IP address.
Any resources created within your private subnet, for example your backend databases, would be considered private and inaccessible by default from the Internet. There’s two changes you need to make to your infrastructure to make a subnet public,
- Add an Internet gateway(IGW): It is a managed component by AWS that is attached to your VPC and acts as a gateway between your VPC and the outside world.
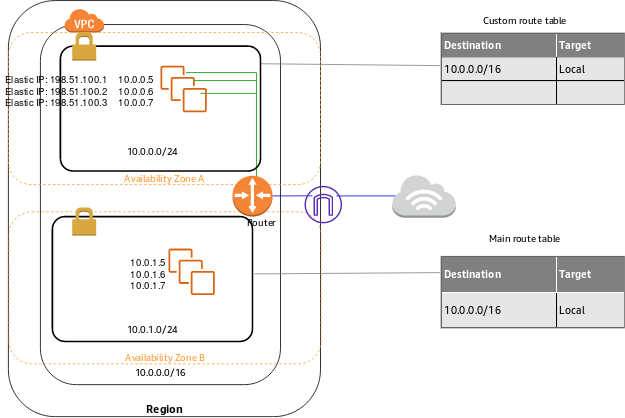
- Add a route to the public subnet’s route table: Every subnet when it’s created will also be an associated route table. You can have the same route table associated to multiple subnets. You can’t associate more than one route table to a single subnet.
By default, when your subnet’s created, it will have a default route in it, and this is a local route. Every route table has this local route. It can’t be deleted, and it simply allows all subnets within your VPC to communicate with each other.
When working with TCP/IP addresses within your subnet, first four addresses in any subnet are reserved and you cannot use for host addresses and also the very last address is reserved. So that’s why use only 251 IP addresses available to you that you can use to assign to your host resources from 256 IP addresses.
It’s not best practice to deploy all of your resources within the same availability zone, within a single region, simply because it doesn’t offer high-availability and resilience.
For more information about Subnets,
- https://docs.aws.amazon.com/vpc/latest/userguide/VPC_Subnets.html
- https://docs.aws.amazon.com/vpc/latest/userguide/working-with-vpcs.html
- https://docs.aws.amazon.com/vpc/latest/userguide/default-vpc.html
Q. What do you mean by VPC Peering?
We can allow VPC peering to allow VPCs to communicate with each other. Now the peering connection that links the two VPCs is actually run and hosted on the AWS infrastructure.
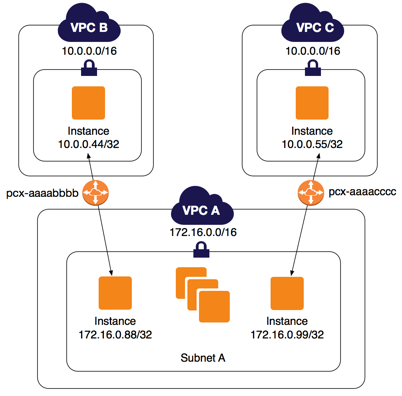
Now it’s important to mention that this peering connection is a one-to-one connection only.
When you create VPC peering connections, each VPC cannot have an IP address overlap between them. You can have VPC peering configured between the same region or between different regions.
Is there a better alternative than one to one connection?
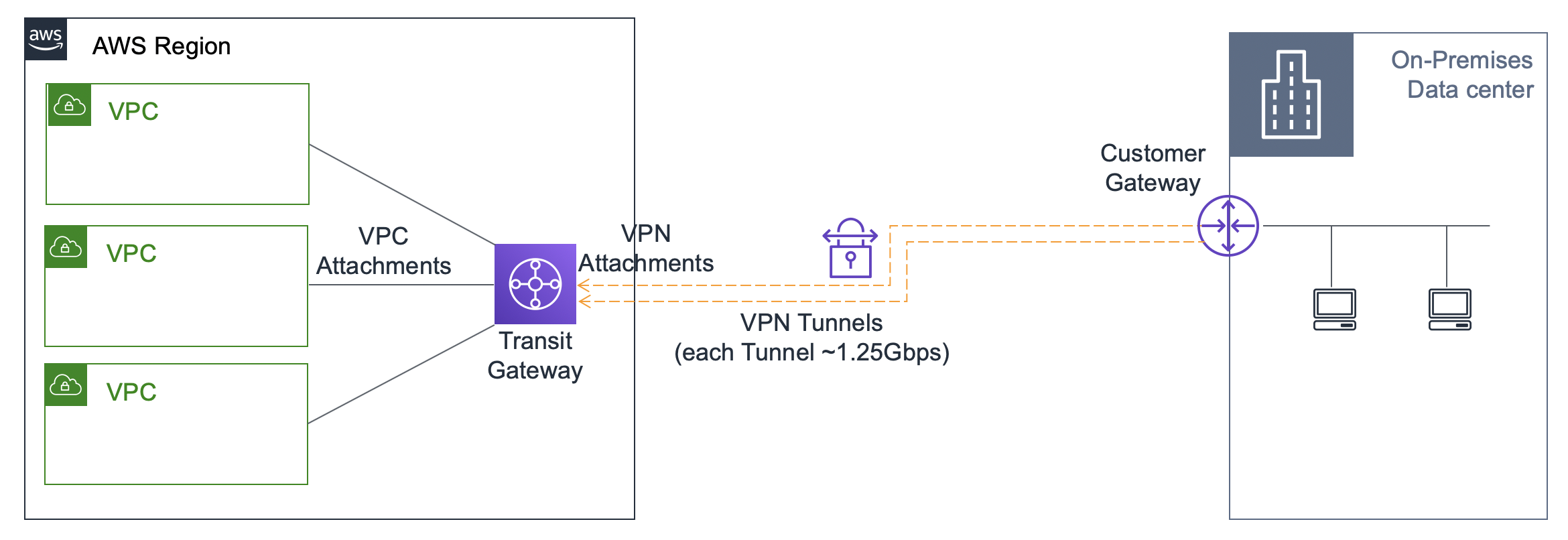
AWS Transit Gateway simplifies your whole network connectivity. It allows all of your VPCs to easily communicate with one another and also communicate with your remote locations as well.
All the routing is managed centrally within that hub and when any new remote locations or VPCs are created.
Now because the Transit Gateway goes through this central hub, it allows you to centralize all your monitoring as well for your network traffic and connectivity all through the one dashboard which is great.
For more information about VPC peering and AWS Transit Gateway,
- https://docs.aws.amazon.com/vpc/latest/peering/what-is-vpc-peering.html
- https://docs.aws.amazon.com/vpc/latest/userguide/vpc-peering.html
- https://aws.amazon.com/transit-gateway/?whats-new-cards.sort-by=item.additionalFields.postDateTime&whats-new-cards.sort-order=desc
- https://docs.aws.amazon.com/vpc/latest/tgw/what-is-transit-gateway.html
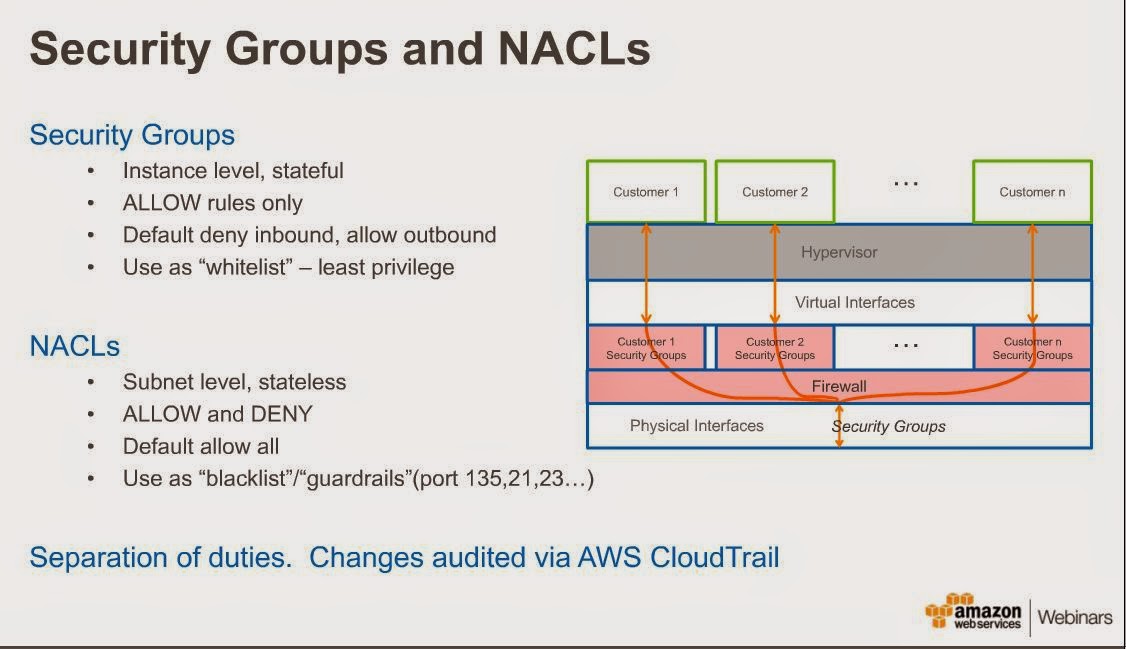
Q. What do you mean by network access control lists(NACLs)?
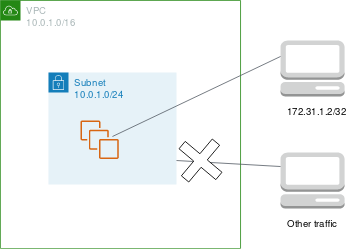
They are essentially virtual network-level firewalls that are associated to each and every subnet, and they help to control both ingress and egress traffic moving in and out of your VPC and between your subnets.
Whenever you create a new subnet, it will also associate a network access control list. Now by default, NACL will allow all traffic, both inbound and outbound, so it’s not very secure.
The rule numbers allow you to specify what order the rules will appear inside the NACL, and as soon as traffic hits one of these rule where it matches all of the type, protocol, port range, … it will carry out the action at the end, whether that is allow or deny.
NACLs are stateless this means that any response traffic generated from a request will have to be explicitly allowed and configured in either the inbound or the outbound ruleset, depending on where the response is coming from.
For more information about NACLs,
- https://docs.aws.amazon.com/vpc/latest/userguide/vpc-network-acls.html
- https://docs.aws.amazon.com/vpc/latest/tgw/tgw-nacls.html
- https://medium.com/kernel-space/when-to-use-security-groups-and-nacl-in-aws-e6a320ca0734
Q. What do you mean by Security groups?
They are similar to NACLs where they filter traffic both inbound and outbound but whereas NACLs worked at the subnet level, security groups work at the instance level.
There’s no rule number with the security group, so with security groups, if there’s a rule in there, then it’s considered allowed, if there’s no rule, then all traffic is dropped by default,
Security groups are stateful which means you don’t have to configure specific rules to allow return traffic from requests like you have to do with NACLs.
- The NACLs are used for the subnet and network layer.
- The security groups are used at the instance layer.
For more information about Security Groups,
- https://docs.aws.amazon.com/vpc/latest/userguide/VPC_SecurityGroups.html
- https://docs.aws.amazon.com/AWSEC2/latest/UserGuide/default-custom-security-groups.html
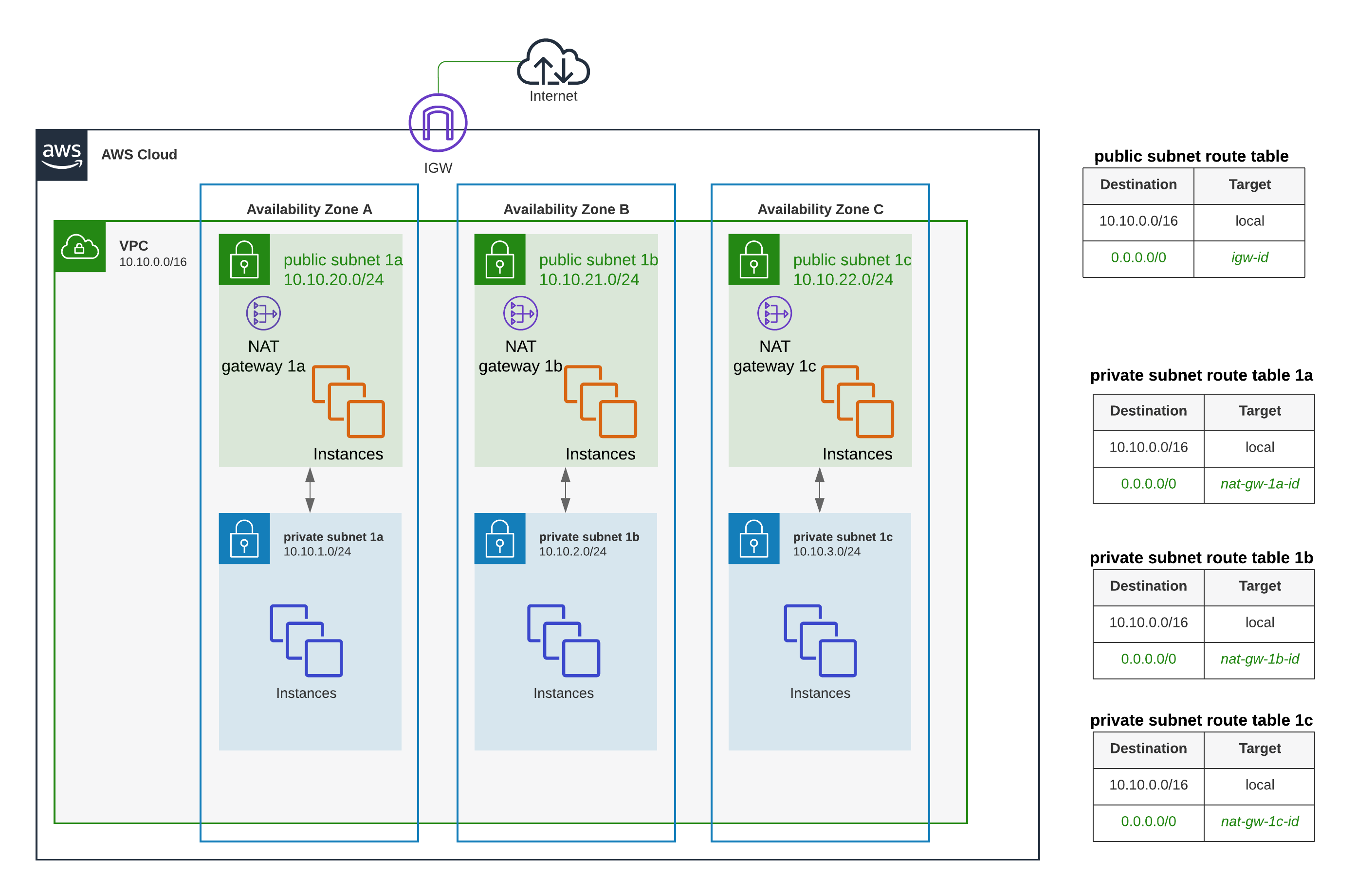
Q. What do you mean by Nat Gateway?
We have the responsibility of maintaining the operating systems of our EC2 instances, then we need to be able to download updates. However, this subnet is private. So it has no access to the Internet gateway, and therefore the Internet, so how can we download those updates?
A NAT gateway sits within the public subnet. Because it sits within the public subnet, it has to have a public IP address in the form of an Elastic IP address(EIP), and this is assigned to the instance itself. Now because it sits within the public subnet, it has a route out to the Internet gateway, and to the Internet.
Now once we have our NAT gateway set up and configured, we need to update the route table of our private subnet.

This NAT gateway will then take the request, go via the Internet gateway, and download the appropriate software that’s required, and send it back to the EC2 instance requesting it.
A NAT gateway, is that it will not accept any inbound communication initiated from the Internet. It will only accept outbound communications originating from within your VPC. So it will deny all inbound traffic that’s been initiated from the Internet.
The NAT gateway itself is managed by AWS. It’s very easy to do, you simply create the NAT gateway, specify what subnet it should reside in, and associate an Elastic IP address, and AWS will manage all other configuration. So if you have multiple public subnets in different Availability Zones, you will need to set up another NAT gateway within that subnet as well. AWS will not automatically deploy a NAT gateway within each of your public subnets.
For more information about NAT Gateway,
- https://docs.aws.amazon.com/vpc/latest/userguide/vpc-nat-gateway.html
- https://aws.amazon.com/premiumsupport/knowledge-center/nat-gateway-vpc-private-subnet/
Q. What do you mean by Bastion Hosts?
Consider a scenario where you might have EC2 instances sitting in a private subnet, but you want to be able to gain access to those instances from somewhere else on the internet. But because they’re sitting in the private subnet, how can you do that?
The bastion host sits within the public subnet and this is just another EC2 instance. This instance has to follow best practices and needs to be very secure.

Using this as a jump server and connect from the bastion host through to our instances in private subnet using SSH.
The connection process is,
- The engineer will be able to connect to our bastion host using the private key.
- So the engineer will SSH on port 22 to our bastion host, so it’ll connect via the internet. The connection will then come through the internet gateway.
- The security group says, allow connection if it’s an SSH connection from this IP address of our engineer.
- The engineer has access to our bastion host. But now, our engineer needs to jump across to our private instances. We’re going to need a private key to do that.
We don’t install private keys within the public subnet or on the bastion host because if this bastion host ever got compromised, then the malicious user will be able to use any private keys to connect to our private subnet instances.
SSH agent forwarding: allows us you to do is to store the private keys for the instances within the private subnet on your local client, so that when you connect through to the bastion host, you can then SSH, but using the private key to the EC2 instances that is stored on your client.

For more information about bastion hosts,
- https://docs.aws.amazon.com/quickstart/latest/linux-bastion/overview.html
- https://docs.aws.amazon.com/quickstart/latest/linux-bastion/architecture.html
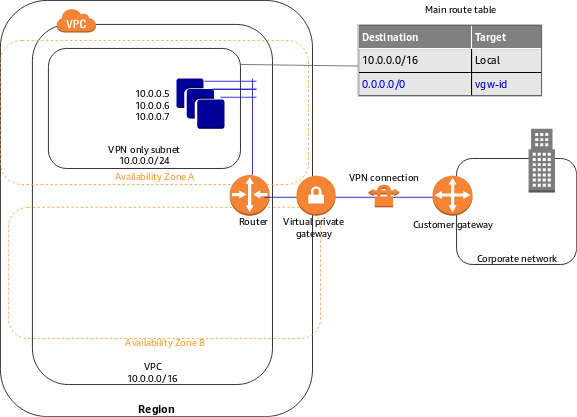
Q. How to connect to on-premises networks?
A.VPN connection:
Virtual Private Network is essentially a secure way of connecting two remote networks across the internet
We want to enable communications between our resources in our private subnet in our VPC in AWS and to resources that are held on premise within our data center.
- On your VPC side, you need to create something called a virtual gateway and attach it directly to your VPC. This is managed by AWS.
- In our data center, we also need another endpoint and this will be our customer gateway.
Now once your virtual private gateway is attached to your VPC and configured and also your customer gateway’s installed, then what we do is initiate a tunnel between the two endpoints. This VPN tunnel can only be initiated from your customer gateway. It can’t be initiated from your virtual gateway.
We have our VPN tunnel up and running created between our virtual private gateway and our customer gateway, we need to change the route table associated to this private subnet. You can also enable route propagation within your route table as well.
For more information on AWS VPN,
- https://aws.amazon.com/vpn/
- https://docs.aws.amazon.com/vpc/latest/userguide/vpn-connections.html
- https://docs.aws.amazon.com/vpn/latest/s2svpn/VPNTunnels.html
B.Direct Connect:
Now whereas your VPN connection used the internet to get to your VPC, a Direct Connect connection doesn’t traverse the internet. Instead it uses private infrastructure and connects directly to your VPC. So, there’s no public network that the traffic traverses.
- Within our data center, we’ll have a router.
- Now with a Direct Connect location, there’s a middle entity before you get to AWS infrastructure, now this is usually an AWS partner or an AWS customer that holds Direct Connect infrastructure and there’s two parts to this.
- There will also be a router in the AWS side as well.
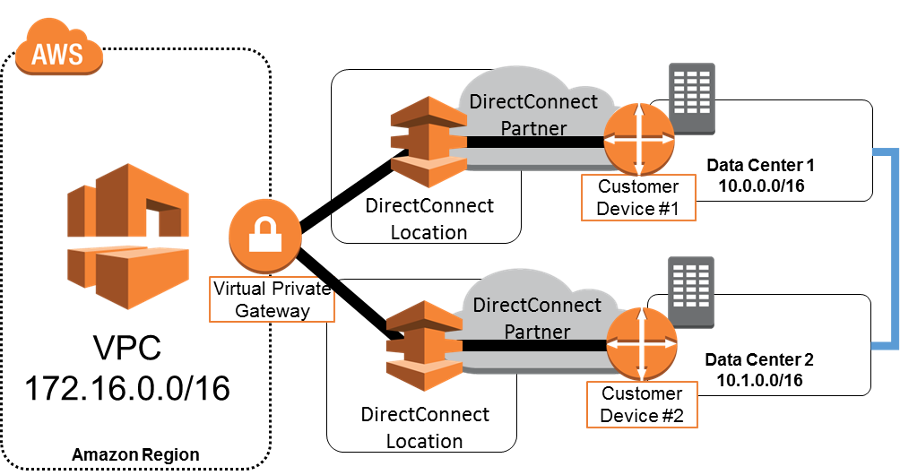
AWS Direct Connect, it enables you to create a connection between your data center and an AWS region, not just a VPC, it’s actually connected to a defined region. The reason it’s connected to a region and not a VPC is that a Direct Connect connection allows you to access public as as private resources.
For more information about AWS Direct Connect,
- https://aws.amazon.com/directconnect/
- https://docs.aws.amazon.com/directconnect/latest/UserGuide/Welcome.html
- https://docs.aws.amazon.com/directconnect/latest/UserGuide/direct-connect-gateways-intro.html
Other AWS services you should know about
A.Route 53:
Route 53 is Amazon’s highly available and scalable domain name system that provides secure and reliable routing of requests, both for services within AWS and infrastructure that is outside of AWS.
Route 53 is able to provide this service through its global network of authoritative DNS servers that reduce latency and can be managed via the management console or API.
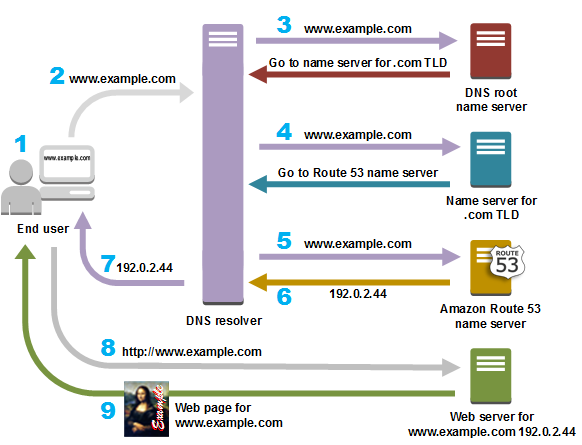
To understand Route 53, let me explain some of the components and elements used within the service,
- A hosted zone is a container that holds information about how you want to route traffic for a domain.
- Different domains
- Resource record types
- Routing Policies. When you create a resource record set, you must choose a routing policy that will be applied to it, and this then determines how Route 53 will respond to these queries.
For more information about AWS Route 53,
- https://aws.amazon.com/route53/
- https://aws.amazon.com/route53/features/
- https://docs.aws.amazon.com/Route53/latest/DeveloperGuide/Welcome.html
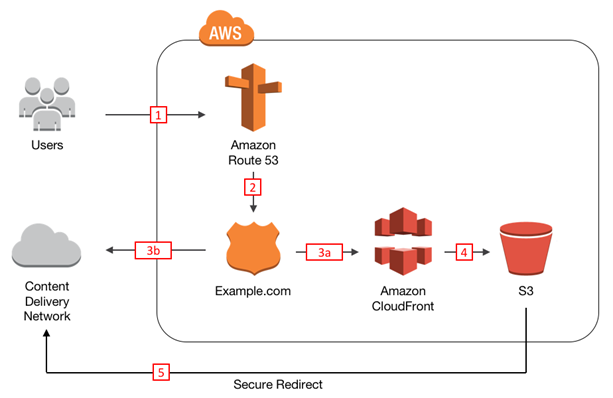
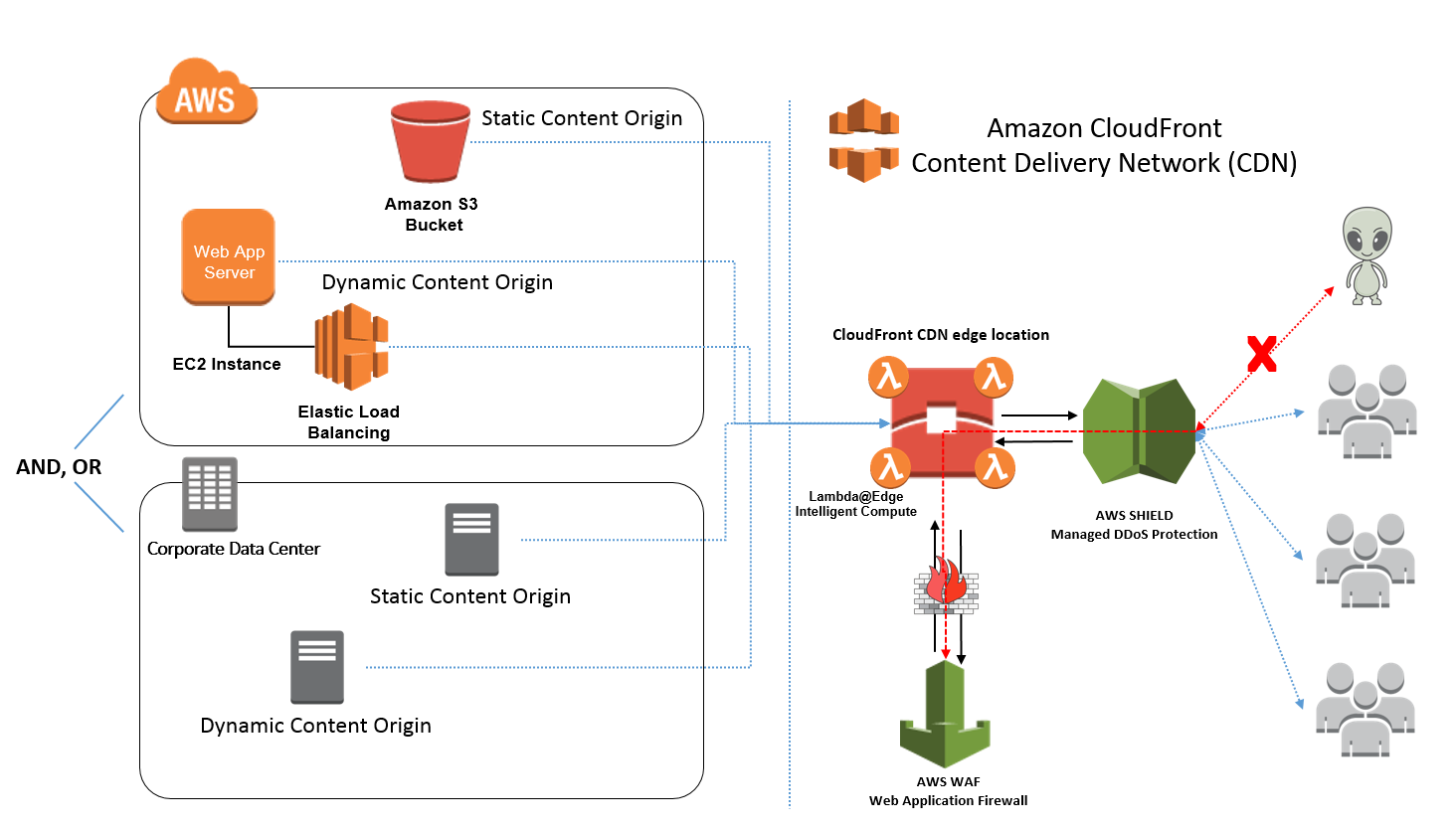
B. AWS Cloud front:
Amazon CloudFront is AWS’s fault-tolerant and globally scalable content delivery network service. It provides seamless integration with other Amazon Web Services services to provide an easy way to distribute content.
- Amazon CloudFront speeds up distribution of your static and dynamic content through its worldwide network of edge locations.
- AWS CloudFront doesn’t provide durability of your data. Instead, it distributes the source data which resides on durable storage, such as Amazon S3.
AWS edge locations are sites deployed in major cities and highly populated areas across the globe. While edge locations are not used to deploy your main infrastructure, such as EC2 instances or EBS storage, they are used by AWS services such as AWS CloudFront to cache data and reduce latency for end user access.
Once your distribution is configured and enabled,
- When content from your website is accessed, the end-user will be directed to their closest edge location in terms of latency
- if the content is cached by CloudFront at that edge location. If the content is there, the user will access the content from the edge location instead of the origin, therefore reducing latency.
- If the content is not there, or the cache has expired for that content at the edge location, then CloudFront will request the content from the source origin again.
- This content will then be used to maintain a fresh cache for any future request until it again expires.
For more information on basics of computer networking, https://programmerprodigy.code.blog/2021/01/19/how-does-modern-computer-networking-work/
I will be spending the next couple of weeks focusing on AWS Management techniques. Let me know where I could improve?

